Revamped & Ready: Introducing the New Developer-First LoginRadius Website
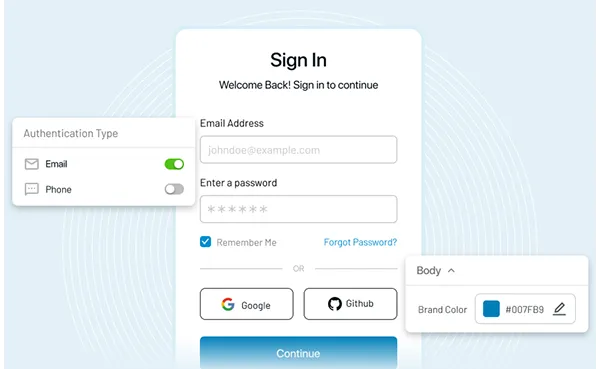
LoginRadius’ vision is to give developers a product that simplifies identity management so they can focus on building, deploying, and scaling their applications. To enhance this experience, we’ve redesigned our website interface, making navigation more intuitive and reassuring that essential resources are easily accessible.








![The Death of Passwords [Infographic]](/static/d6212ca7d6363d9be407c8985a16cc20/7f8e9/death-of-passwords.webp)